In brief: Microsoft’s ElectionGuard is sophisticated technology that gives the public (e.g., voters, parties) the ability to detect signs of electronic vote tampering. This essay describes that product and its live-election test in Fulton, Wisconsin in February 2020. There are two take-away points.
First: Even if ElectionGuard successfully alerts its users to signs of trouble, election officials are unprepared to respond to those signs. We must disabuse ourselves of the fantasy that more or newer or shinier technology, by itself, can compensate for vulnerabilities that exist when no human takes managerial responsibility for the accuracy of the certified results.
Second: The trial run in Fulton created a rare circumstance: On this one day, in this one polling place, the managers in charge were truly committed to producing results of unquestionable accuracy—with no excuses, no whining, no blue smoke or mirrors. And they did, using two simple methods. The critical lesson of Fulton is this: When election managers truly want to, they can produce verified accurate results with minimal additional work and no new technology.
Captain Chesley (Sully) Sullenberger became the face of technology mastery when in January 2009 he safely landed 155 people in the Hudson River after his aircraft did not, shall we say, perform as expected. Later he commented:
“What we have learned is that automation does not decrease problems. It changes the nature of problems. As we use more and more technology in the cockpit, we must always make sure that humans are in complete control of the aircraft and its flight path.”
When it comes to election automation, Americans have not yet learned that lesson. On that future Election Night when the voting machines deliver incorrect vote totals, the election will crash and burn, because our officials are not prepared to take effective control to save it.

It’s a sign of America’s deep-seated desire to trust technology that many readers will dismiss this message unless I remind them of three basic and irrefutable facts.
- First, any computer can be deliberately misprogrammed. Therefore, all voting systems are hackable, either by outsiders or by corrupt insiders. Insiders include the employees and contractors working for voting equipment vendors, service companies, and the local election offices.
- Second, there is no surefire way to prevent all misprogramming, no matter how big the company or how lush the security budget. Computer systems of global corporations as big as Sony and as focused as the US Department of Homeland Security have been compromised.
- Finally, American voting-machine companies and our local election clerks have nowhere near the security resources of Sony or the DHS. Not even close. Knowing that malefactors found their way into those systems, it is delusional to imagine voting-equipment companies and town clerks can keep them out of our voting machines forever.
Therefore, responsible citizens accept the inevitable: Sooner or later, American voting machines will be deliberately programmed to miscount on Election Day.
And when that happens, as with US Airways Flight 1549, it will be human actions, not technology, that can save the election. If local officials quickly detect the miscounts and decisively correct them before certification, the election will be saved. If they do not, the election will be a total loss.
However, in most states including Wisconsin, election officials trust the voting machines and the programmers. Full stop. They make no effort to detect outcome-altering miscounts; they have no plans in place to correct the results if miscounts make themselves known. Occasionally, Wisconsin officials check a few randomly selected voting machines’ tallies against the paper ballots, but even if those audits notice one miscounting machine, the officials do not expand the audit to verify the outcome and do not claim to.
In short, we have no Captain Sullenbergers in the cockpit of our elections.
Josh Benaloh, Ph.D., Senior Cryptographer for Microsoft, thinks he has an antidote to the officials’ managerial passivity: Technology that will enable other people to detect miscounts. Staying with the Sullenberger analogy, he wants to enable each passenger independently to monitor the plane’s engine power and altitude.
It’s easy to trust Benaloh’s motives and his expertise. With boy-next-door good looks, Benaloh’s face carries a natural smile that disappears only when he frowns—and sometimes not even then. As whip-smart as they come, Benaloh has degrees from Massachusetts Institute of Technology and Yale, and his credentials as a forward-thinking innovator are impeccable: He wrote his doctoral dissertation on verifiable secret-ballot elections in 1987, more than a decade before computerized vote-counting was common, and three decades before election security came into public view as a serious concern. Ask anyone in the field to name the top 10 US experts, and Benaloh’s name is likely to be on their list.

Benaloh and I were among those present in Fulton, Wisconsin last February when a small election (only two races on the ballot) allowed the Microsoft team to demonstrate ElectionGuard, an election-security product Benaloh helped to develop with the company’s Defending Democracy program. He and I spoke in total for more than two hours that day, during which he explained to me the purpose of ElectionGuard and the basics of how it works.
ElectionGuard is not a voting machine itself, but a program that can be installed on other voting systems, to work in parallel with them. In brief, ElectionGuard will enable voting systems to print a receipt for each voter. The voter will cast the ballot as usual and leave with the receipt, which contains a ballot-tracking code. Later, they can visit a website, enter the code, and get a message: “Your vote was counted!” In addition, because Microsoft is providing the tabulation software free to the public, it will allow others—most likely, candidates’ campaigns—independently to verify the vote totals if they can get the electronic ballot files from the local officials.
Benaloh convinced me that ElectionGuard’s use of advanced encryption methods will make it impossible for anyone to alter the digital record of the votes without leaving obvious evidence, which voters will be able to detect when they enter their ballot-tracking codes.
What he did not convince me of, to his polite but visible frustration that day, was that ElectionGuard will secure our election results or build voter confidence. (See note #1, at the end of this post.) But that’s nothing Benaloh’s inventions or Microsoft’s products can do, any more than Flight 1549’s cockpit dials could have landed that plane safely in the river if Captain Sullenberger not been ready and able to take charge.
To understand the types of miscounts that ElectionGuard is designed to detect, we need to understand voting-machine systems’ programmable components.
For the Fulton demonstration, equipment was provided by VotingWorks, a young nonprofit, open-source election-equipment vendor based in San Francisco. Benaloh told me that ElectionGuard can be used with hand-marked paper ballot systems, but for the Fulton set-up, voters used touchscreens, rather than pen-and-ink, to indicate their selections. The system included three main components:
- A ballot-marking device (BMD) is a computer that displays the races and candidates to each voter on a touchscreen monitor. As voters make their selections by touching the display, the BMD translates those touches into digital data, which is transferred to…
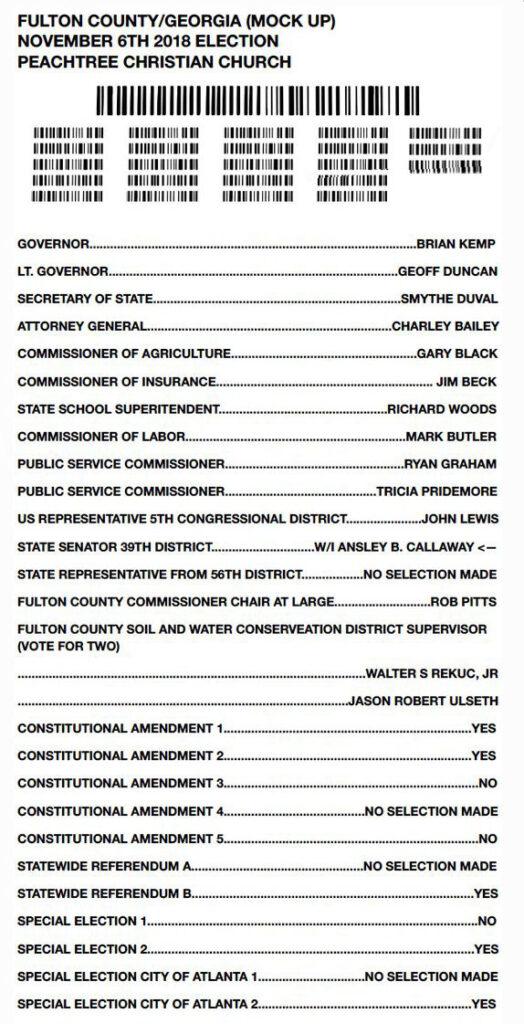
- A printer that produces a paper ballot. The paper ballot used in the Fulton demonstration was of the type that prints votes two ways—once in encoded data (in this case, a QR code) that will be counted, and separately in human-readable text that will not. The voter takes the printed ballot and inserts it into…
- A tabulator—which reads the votes encoded in the QR code, and records them in a digital file, along with all the other ballots it has read. At the end of the day, the tabulator will tally the votes for each candidate and print the totals on a poll tape. The tabulator might also transmit the vote totals to a central computer to be compiled with results from other polling places.
In normal use (though not in the Fulton demonstration), that whole set-up is managed through:
- A central elections management computer, which in Wisconsin is operated by the county clerk. As the conduit for the software that is installed in the polling-place equipment, these central computers are the most attractive target for malicious interference. For example, if a malefactor bribed a technician to install remote-access capability on Milwaukee County’s election management computer at some time in the past, that malefactor could alter the software on any or all of the hundreds of pieces of voting equipment in that county.

What types of hacks is ElectionGuard designed to detect?
Malefactors have two high-level options: They can create chaos with obvious malfunctions, or they can alter results while trying to postpone or escape detection.
Chaos-seeking malefactors might do things such as prevent the equipment from powering up on Election Day; make the BMDs print ballots the tabulators cannot read; or make the tabulators produce nonsensical results on Election Night. When the malefactor has already made sure the problem will be obvious, ElectionGuard’s detection is not needed. Nor does ElectionGuard give managers any new options for responding to chaos.
But what if the malefactors try to postpone or even escape detection? In that case, ElectionGuard might or might not help. It depends on whether the malefactor hacked the BMD or the tabulator.
Because ElectionGuard relies on the BMD’s digital interpretation of the votes, it cannot detect hacks that made the BMD misinterpret input (that is, the voters’ touches.) If the BMD misinterprets a touch on Alexander Hamilton’s name as a vote for Aaron Burr, ElectionGuard will, too. (Benaloh disagrees with this statement. See note #2.)
However, if the malefactor works with the tabulator rather than the BMD, ElectionGuard can enable detection.
When a voter inserts the paper ballot into the tabulator (with or without ElectionGuard), the tabulator interprets the votes recorded on that ballot; internally creates a digital record of each vote; and uses that record to tally results at the end of the day.
One of the ways a malefactor might intervene is this process is to make the tabulator look at the ballots with votes for Hamilton and record some of them, in its own memory, as votes for Burr. Then when the machine tallies the votes at the end of the day, Burr would be credited with some of Hamilton’s votes.
Without ElectionGuard, hand-counted audits are the only way to detect that problem. But when BMDs are equipped with ElectionGuard, each voter gets a separate, printed receipt with their ballot, as shown below. The ballot has a unique ballot ID number, and the receipt has a unique ballot tracking code, allowing ElectionGuard to match the two.

When the voters inserted their ballots into the tabulator, the tabulator worked as it normally would have without ElectionGuard, while ElectionGuard created a separate electronic record of the votes, in encrypted form, tagged with the unique tracking code.
Later, after Election Day, the voters are able to visit a website, enter their tracking code, and see a message. (Benaloh’s thoughts about who should host this website are in Note #3.) If the ElectionGuard record of that ballot matches the tabulator’s, the voter will see “Your vote was counted!” (That is all it will tell them; it does not reveal even to the voter which candidate received the votes.) If the tabulator’s interpretation of the votes did not match the votes that ElectionGuard recorded, the voter would not receive the confirmation message.
And then what?
Well, that’s up to the election officials. Voters will start reporting problems the day following the election. Your guess is as good as mine about how many such reports each clerk will need before he or she stops assuming voter error and starts to question whether the equipment might be at fault. There is nothing in Wisconsin law or practice that requires clerks to take voters’ reports seriously.
Nor does anyone know what the clerks will do if they believe the voters’ reports of trouble—not even the clerks. Captain Sullenberger knew what to do when he realized his plane had lost its engines. But our election ‘pilots’ trust their voting equipment so completely that they fly without emergency procedures.
Another way a malefactor might intervene would be to allow the tabulator to record the individual votes correctly in its own memory, but cause it to produce incorrect vote totals at the end of the day. That is, if 60% of the ballots contained a vote for Hamilton, the tabulator would correctly record each individual vote in its memory, but at the end of the day produce vote totals showing 60% of the votes going to Burr. In that case, ElectionGuard would tell every individual voter “Your vote was counted!,” which is, I suppose, true-ish.
But ElectionGuard could reveal that problem in a different way, to anyone who looks for it. Its open-source code enables anyone with programming skills to create their own verification tool. So if campaigns or political parties can get the election’s digital ballot files from the election officials, they will be able to tabulate the votes themselves. Microsoft will provide, free of charge, the source code needed to write those tabulation programs, even while the votes remain encrypted.
Currently, no one in Wisconsin verifies computer-generated vote totals, so ElectionGuard would be an improvement.
But will independent tabulation using ElectionGuard ever save a miscounted election–even if it detects the problem? Probably not. At most, it will provoke expensive but futile lawsuits. The miscount won’t be corrected for at least two reasons, neither of which can be solved by Microsoft.
First, it is highly unlikely election officials will allow access to the ballot files until after the results have been officially and finally certified, at which point no corrections are legally possible. And because there is no chance that a re-tabulation would lead to a correction, campaigns will be unlikely to bother. Benaloh agrees: “There would be minimal value in using ElectionGuard in a situation in which the election record is not made public until after certification.”
Second, even if clerks do release the ballot files immediately following Election Day, unofficial audits have no standing. Citizens’ reports of miscounts are ignored. When such groups have documented miscounts in the past, officials did nothing; the press yawned; and the results were not corrected. Our election laws and our election officials do not recognize that voters have any standing to question the results.
If one of the candidates’ campaigns used ElectionGuard to detect a miscount, there might be more sound and fury than if citizens used it, but still no correction. Imagine, for example, that the Trump campaign had been able to use ElectionGuard in November 2020. If they had announced they’d found a miscount, officials would have issued statements saying that the campaign must have done it wrong. The Biden campaign would not have done their own re-tabulation; there is no reason why an Election-Night winner ever would. Instead, the Biden campaign, the officials, and the press would have insisted, correctly, that the Trump campaign’s only legal recourse was to demand a recount.
Unlike most candidates, Trump was able to force a partial recount, but that’s a rare situation. Recounts in Wisconsin are available only to second-place candidates who lose by less than a 1% margin, and even they must be able to pay the full estimated (and inflated) cost of the recount upfront in cash, unless they lost by less than 0.25%. Wisconsin Republicans will remember that, as close as the 2018 governor’s race was, and as widespread as concerns were about the City of Milwaukee’s atypical reporting, Scott Walker’s 1.1% loss margin prohibited him from even petitioning for a recount. ElectionGuard cannot change that.
In addition, a Wisconsin recount would be performed by running the ballots back through tabulators that have been ‘reprogrammed’ only to prevent them from printing out results for any but the recounted race. The tabulators’ second count would agree with the first and be accepted as confirmation, and the ElectionGuard results would be dismissed. When the buzzer sounds for the certification process, the victory will go to the malefactors.
So, sure, yeah. We can install ElectionGuard on America’s voting systems, and it will do no harm. When an election is hacked, it will be as helpful to voters as a set of cockpit dials on each seat back would have been for the passengers on Flight 1549: “Notice: This plane has lost all engine power.”
On that day, as with the Miracle on the Hudson, the only way to save the election will be for the professionals in the cockpit to take decisive, competent, manual control and bring the thing in for a safe, if atypical, landing.
Captain Sullenberger was prepared to do that. Our election clerks are not.
Fortunately, that is not the whole story. The Fulton demonstration did show how American election officials can make sure only correct winners are certified. It showed us what happens when those in control of the voting equipment really, truly, desperately, and sincerely want accurate election results. And that is the most important lesson of the Fulton demonstration.
When running a normal election (that is, when they are not demonstrating or testing new technology), officials need only to produce credible results. Notice I did not say accurate results. Fact is, they don’t normally have to prove accuracy to anyone, not even themselves.
In that respect, the Fulton demonstration was a unique situation and uniquely instructive. Microsoft spent years and hundreds of thousands of dollars, drawing upon some of the best cyber-talent in the nation to develop ElectionGuard. For its first public demonstration, the organizers could not simply say “We believe the results are accurate because we trust the computers and you should, too.” In Fulton, they knew they had to prove accuracy. Otherwise, the whole thing would have been an embarrassing waste of time.
So they managed the polling place in a way that produced rock-solid results of unimpeachable accuracy. Such a thing is possible, and election officials know it.
That effort required only two easy safeguards—one that verified BMD performance, and one that verified the tabulator. Neither used any new technology.
I’ll let Microsoft tell you about the safeguard that checked the tabulator’s accuracy:
“One of the things we wanted to do was … to make sure that the voters would never have to question that the results were accurate. There would be a hand-count of the paper ballots at the end of the day as the officially certified result. It took the poll workers maybe only 15 minutes to actually count the votes. We compared all three results (the voting-machine poll tape, the ElectionGuard tabulation, and the hand count) and all three matched, which was exactly what we were going for.”
Yes, when Microsoft the Global Tech Giant knew it had to produce accurate election results—leaving no shadow of a doubt—they hand-counted paper ballots. Or, more precisely, they counted the votes using two different methods and compared the results to make sure they matched.
It took them only 15 extra minutes. In larger elections, officials would not need to count every vote to verify the correct winner: Election authorities have developed methods that allow officials to confirm the right winners by hand-counting only a small sample of ballots—much like an exit poll that looks at ballots instead of interviewing voters.
But what about the BMD? How did the Fulton demonstrators ensure that the computer-generated ballots were accurate records of the voters’ selections?
Verifying ballots’ accuracy is not an issue when voters mark their own ballots with a pen. If no vote is recorded as the voter touches pen to paper, the voters notice and tell the poll workers that the pen is out of ink. And if a voter touched a pen to one oval and a different oval turned black, the voters would positively flip out.
But when voters make their selections by touching a display on a computer monitor, it’s possible that the printed ballot could be missing votes or contain votes printed for the wrong candidate. Auditors and recounters are helpless to detect misprinted ballots because they have no way to know what the actual selections were. Only the voter can notice if that happens.
But touchscreen-using voters don’t review their printed ballots naturally, as hand-marking voters do. They need to be instructed or they will not do it. For example, both the cities of Madison and Milwaukee make heavy use of BMDs, but neither city instructs voters to verify the ballots. During the November 2020 election in those cities, I observed around 200 voters at six polling places as they used BMDs in early voting. Not one verified their printed ballot. If misprogramming or malfunction caused those BMDs to print any incorrect votes, no one will ever know and the true votes are lost forever.
To ensure that all Fulton ballots were voter-verified, organizers set up a ‘verification station’ between the printer and the tabulator, where a poll worker intercepted every voter and reminded them to read their ballot and make sure it was correct. With only two races on the ballot, every one of the 398 voters was willing and able to do that.
But even with 100% voter verification, the Fulton event showed how election officials might allow voters to use a hacked BMD all day in a Wisconsin polling place. Four of the Fulton voters—slightly over 1 percent—noticed and reported incorrect votes. In each case, the voter and poll worker immediately assumed it was voter error—with no effort to rule out machine malfunction. But was it? Probably, but no one will ever know for sure.
Managers with a passing level of quality-assurance expertise would not simply assume voter error, but would always be alert for misprinting BMDs. They would keep track of the number of voters reporting misprinted ballots; they would have decided ahead of time how many misprints would be considered indicative of a malfunctioning machine; and they would be prepared to take that BMD out of service.
But few real-world election officials are acquainted with real-world quality-assurance principles. Wherever BMDs are used in Wisconsin, the assumption is as it was in Fulton—to blame voter error for every noticed problem. If ever, say, 10% or more of the BMD-using voters at a polling place report misprinted ballots, election officials have no backup or recovery plans. Managers can choose to respond to signs of trouble; they can choose to respond in an improvised ineffective way, or they can choose to ignore them.
No technology, including ElectionGuard, can fix that. It’s not a problem with the technology; it’s a problem with the management practices.
A separate issue, which this blog has covered before, is the risky practice of encoding votes in a way that prevents voters from verifying them no matter how closely they study their ballots. ElectionGuard cannot help with that, either. That problem can be corrected only by redesigning the ballots so that the tabulators count the same recorded data that the voters verify, and vice-versa.

not the text the voter is able to verify. If an audit or recount using the votes recorded in the text produces different results than the results the tabulators produced using the votes recorded in the QR codes, and voter verification was not witnessed and documented by poll workers, no one has any way to tell whether the text or the QR code is correct.
We will not be able to secure election results until American voters and officials recognize that it is the officials’ responsibility—not Benaloh’s, not the vendors’, not the voters’, not the candidates’, not the lawyers’—to detect and correct any miscounts.
But it will not be easy to get election officials to accept that responsibility. Whether from naivete or a willful desire to avoid buck-stops-here responsibility, election officials are happy to accept the vendors’ vision that technology can, all by itself, protect elections.
At the Fulton demonstration, I asked both the county clerk and the town clerk why they were willing to cooperate with Microsoft in demonstrating ElectionGuard. What did they see as its potential benefits?
Like election officials everywhere, neither attempted to hide her faith that the voting equipment will always produce accurate results—they will make it clear that they consider such faith a virtue. As a result, they are uninterested in solutions that allow them to detect and correct electronic miscounts because, in their eyes, those miscounts cannot happen.
Instead, their answers focused on two other things: First, encouraging voters to trust the computers as unwarily as they do, and second, reducing their workload. County Clerk Lisa Tollefson told me her reason for hosting the demonstration was that she is “always interested in changes that might make the clerk’s job easier.” Not the answer you’d get from County Clerk Sullenberger.
What about voter confidence? For better or worse, security and voter confidence are separable. True security does not always create voter confidence, and voters can be confident even when security is weak. Both are necessary for well-run elections.
ElectionGuard might increase confidence among those voters who say: “Just give me a receipt for my ballot, and I will believe the election is secure.” They are likely to find it fun to visit a website, plug in a personal ballot-tracking code, and receive the confirmation message “Your vote was counted.”
But the voters’ confidence might fall back to baseline when they realize that ElectionGuard won’t confirm for whom the vote was counted. The stated reason for that is to prevent coercion and the buying and selling of votes, quaint considerations in an age of growing reliance on absentee ballots. (Benaloh shared some good thoughts on ballot privacy – see Note 4.)
Technicians like Benaloh who understand why ElectionGuard is trustworthy will believe the confirmation message is reliable, but they are not the ones for whom such reassurance is intended. Everyone else will be in the same boat they are in now, having to trust the technology and the programmers. My guess is that once ElectionGuard’s novelty wears off, we will be right back where we are now, with skeptical voters being skeptical and trusting voters trusting.
When America finally decides that it really, truly does want secure elections–not just the appearance of security, not just voter confidence–we will stop piling technology upon technology and will instead make sure that that the humans in the election cockpit are responsible and accountable. This is what we will do:
- On Election Day, every voter who can use a pen will create a reliable record of their selections by hand-marking a paper ballot.
- Those ballots will be quickly counted by computers and preliminary results released as soon as possible, just as they are now.
- Promptly following Election Day, the officials will conduct outcome-verifying audits by hand-counting enough of a sample to confirm that the voting machines identified the correct winners. They will be prepared to move quickly to full hand counts in the unlikely event the audit finds the machines were wrong. Only when the computers and the hand counts agree on the correct winners will final election results be certified.
With that simple system—for which our election officials already have all the technology they need—any would-be malefactor will need two entirely different sets of means and opportunity to mess with the results—one to hack the voting machines and the other to manipulate the hand-counted audits. That will deter 99.9% of any manipulation and will detect and correct the rest before the wrong person is sworn into office.
(I’ll give Benaloh the last words; see note #5.)
Notes
#1 – Josh Benaloh graciously and carefully reviewed three drafts (3!) of this blog post, and provided detailed, constructive feedback. I am very grateful. Of course, any remaining errors are mine. There are a few areas where I did not make changes in response to his comments, either because we disagree or because his valid comment didn’t fit into the flow of the argument I wanted to make. These comments provide the basis for the following notes.
#2 – Benaloh wrote: “It is not the case that ElectionGuard ‘cannot detect hacks that made the BMD misinterpret input (that is, the voters’ touches).’ In Fulton, human-readable ballots were produced. Any recording or counting of ballots that was inconstant with this human-readable ballot was detectable. I do not disagree that, in the Fulton instantiation, a voter may fail to notice a misinterpretation that results in a printed ballot that does not match the voter’s selections, and I fully agree that this is a legitimate concern. However, I think that there is an important distinction between “undetected” and “undetectable ” – especially in this context.”
#3 – Regarding the hosting of the website that voters would visit to use their verification codes, Benaloh wrote: “I see minimal value in an individual voter going to an official election website to confirm a verification code. Instead, I would envision third parties such as political parties, media, and watchdogs hosting copies of the election record against which voters could query. There is far more value to me in having my preferred candidate or media outlet confirm that my vote is correctly included in the tally than for me to receive that assertion from an election official whom I may not trust. Of course, if I trust no one, I can confirm the entire record – including my vote – entirely on my own. In the small Fulton pilot, we had no leverage to encourage independent entities to establish such services; so the only verifier available was the one hosted by the town.”
#4 – Benaloh wrote: “I see not revealing individual vote contents as far more than a ‘quaint‘ notion. Secret ballots were not introduced in the U.S. until the late nineteenth century, and before that time elections were rife with vote selling and coercion. It would be easy to provide verifiability if we were not concerned about ballot privacy. We could just post verification codes and voter selections without bothering with any encryption. Although it is very difficult to quantify, I’ve seen numerous anecdotes of coercion (especially spousal coercion) associated with routine vote-by-mail and absentee voting. Of course, voting without the benefit of a poll is preferable to not voting at all; but I believe that the protections offered by in person voting are critical to election integrity. Just as you see audited HMPBs as your gold standard, I view verifiable in-person voting as mine.”
#5 – Benaloh wrote: “I agree wholeheartedly with your general thesis – that ultimate control and responsibility should be in the hands of people. ElectionGuard is not intended as a solution but rather as a tool that can be used by election officials and the public to help achieve accurate outcomes. To push on your Sullenberger analogy, when his engines failed he was not devoid of technology and left entirely to his own devices; instead, he was able to exploit other technologies to help him bring his plane a safe landing. A human was, and should be, in ultimate control; but the availability of tools and technologies helped the human in control to overcome adversity. I regard ElectionGuard as nothing more than a tool that can – depending upon the people who use it – be an effective aid or a superfluous nuisance.
“As such, I would posit that your ideal election design – HMPBs followed by a rigorous human audit – is only enhanced by the inclusion of ElectionGuard. This is not just a pointless inclusion in a process that is already as strong as possible. We have a crisis of confidence in U.S. elections today. We have millions of voters who do not believe election results. They do not believe their election officials (e.g.., Brad Raffensperger) and they do not trust their equipment vendors (e.g., Dominion and Smartmatic). As such, they will not trust the results produced by your ideal scenario.
“While I share few of the views of these detractors, I am somewhat sympathetic to the reason for their suspicion. From their perspectives, they gave their ballots to people they don’t trust who used equipment they don’t trust to produce results they don’t trust. If ElectionGuard had been included with the systems they used to vote, they would have had means to confirm the accurate counting of their votes – despite their lack of trust in the people and systems (potentially including a lack of trust in the ElectionGuard component). I’m old enough to remember Reagan’s overused “trust but verify” admonitions. With ElectionGuard, voters can verify without trust. Without it, voters who do not trust their officials and equipment are left with nothing.”